A dusting attack refers to a relatively new kind of malicious activity where hackers and scammers try to gain access to the funds of users by sending tiny amounts of coins to their wallets. The transactional activity of these wallets is then tracked down by the attackers, who perform a combined analysis of different addresses to deanonymize the person or company behind each wallet.
Similar attack occurred in the summer of 2019, when hundreds of thousands of dust transactions were made within Litecoin wallets.
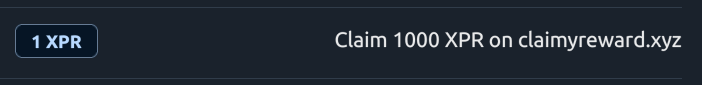
Example of dusting attack:
Fortunately, the source of the attack was identified before any harm was done. They later came forward to state their intention was to advertise their mining pool to the Litecoin community. Despite the harmless outcome, the incident did highlight the ease with which such attacks can be executed – particularly as attempts like the one on Litecoin can happen to any public blockchain.
Generally, attackers have recognized that a large proportion of cryptocurrency users pay very little attention to the almost microscopic amounts of funds they hold in dust.
Once they have dusted a wallet, they will then track data on the activity of the affected accounts in an attempt to uncover what organizations or individuals they are associated with. Hackers may then be able to use that information in phishing scams.
Warning! Never click on suspicious links, especially if contain unknown URL in MEMO.